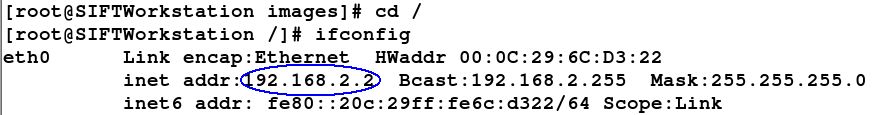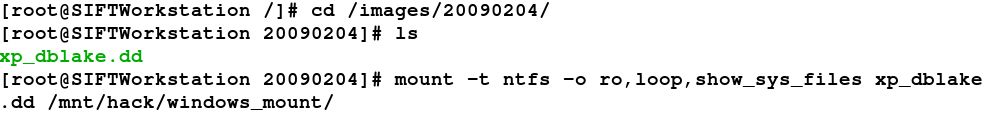
SANS Digital Forensics and Incident Response Blog | Digital Forensic SIFTing: How to perform a read-only mount of filesystem evidence | SANS Institute

SANS Digital Forensics and Incident Response Blog | Digital Forensic SIFTing: How to perform a read-only mount of filesystem evidence | SANS Institute